

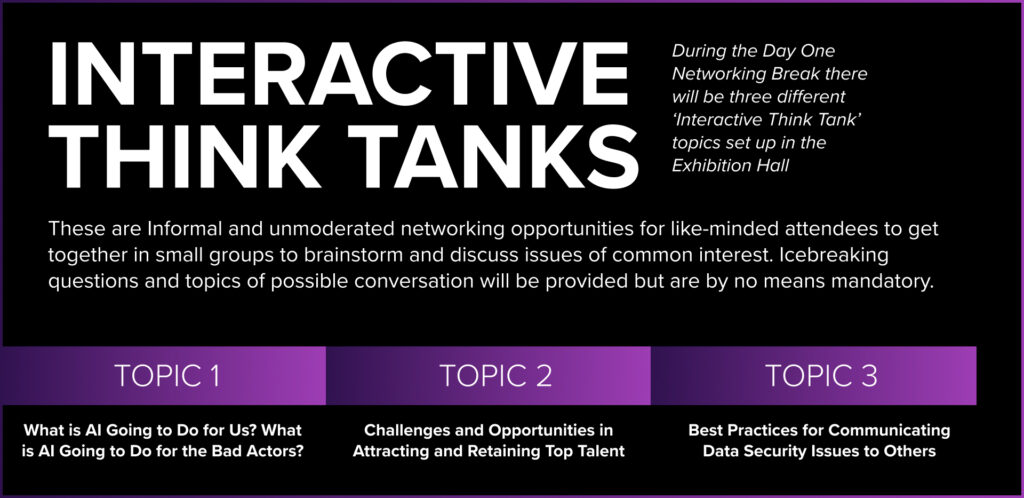
These mutually agreed-upon conversations are arranged and facilitated by Executive Platforms staff to ensure attendees have valuable discussions about their top-of-mind questions, challenges, and opportunities.
This session will focus on critical elements of resilient systems and how to build them. We explore the work of the President’s Council of Advisors on Science and Technology (PCAST) and tie it to Google engineering practices to provide clear examples of how to build resilient systems that run the internet. We’ll discuss 4 critical pillars of cyber resilience and the role they play in fortifying systems against cyber threats in a cyber-physical environment. We’ll discuss the interconnectedness of these pillars and how they form the foundation of a robust cyber resilience strategy.
In this practical workshop, CISOs will learn from real world lessons and come away with a better understanding of:
Cyber threats are more prevalent than ever and security teams are faced with the daunting task of optimizing their security posture while balancing budget, risk, and operational efficiency. With even the most sophisticated security stack plagued with coverage gaps and vulnerabilities, security teams are fatigued and don’t want to add yet another security tool.
Sometimes help comes from an unexpected corner. Modern backup and data security can help IT and security come together and solve problems. Learn what a data security and protection partner like Druva can do to help strengthen your security posture and streamline your incident response and recovery workflows. We will cover:
These mutually agreed-upon conversations are arranged and facilitated by Executive Platforms staff to ensure attendees have valuable discussions about their top-of-mind questions, challenges, and opportunities.

Join us for an insightful discussion on the new AI landscape with Bret Arsenault, CVP, Chief Cybersecurity Advisor at Microsoft. This session will explore the critical aspects of securing AI and delve into the challenges and strategies organizations are facing when it comes to fortifying AI systems and will provide insights into fostering a secure AI landscape while addressing future cybersecurity challenges.
These mutually agreed-upon conversations are arranged and facilitated by Executive Platforms staff to ensure attendees have valuable discussions about their top-of-mind questions, challenges, and opportunities.